





- Home
- BUG SWEEPS
- SEARCH MEATHODS
- WHY US
- SERVICES
-
PRODUCTS

 Technical Surveillance Counter Measures
Technical Surveillance Counter Measures
( TSCM )
CONTACT US
info@technicalprotection.co.uk
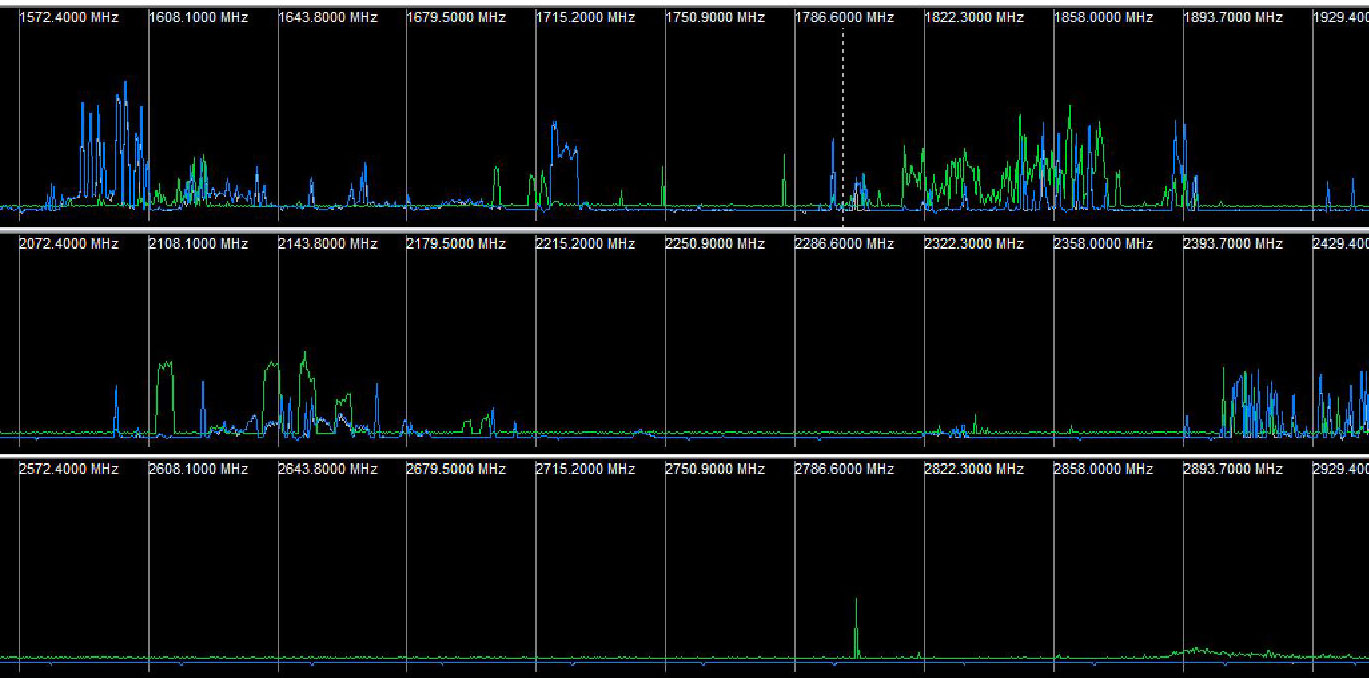
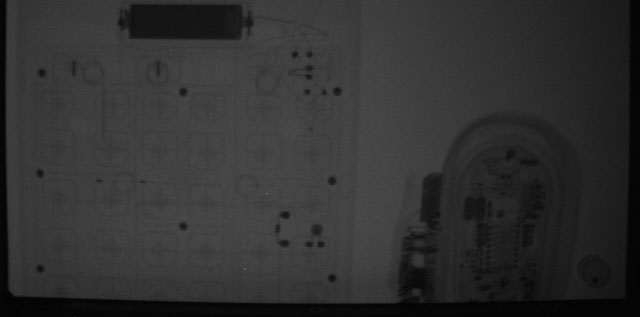
0207 781 9247Information is a valuable asset and needs to be treated as such. You or your company stand to lose substantially when unauthorised access to your communications is possible. Let us protect your valuable information and prevent it from becoming a commodity that can be acquired by your competitors.Technical Protection can supply bespoke security to safeguard companies and private individuals from information theft. We are fully trained and our operatives continue to pursue professional development and familiarity with the latest new GSM and digital based transmitters.During 2008, Technical Protection had a find in one in every 10 TSCM searches; this year we are finding one in 6. Technical Protection offer the same high-quality service we have in the past, simply put-this statistic is proof that electronic eavesdropping, unauthorised communications interception and espionage are a growing threat.They are being used somewhere. Technical Protection operatives are regularly finding these devices during sweeps. Some of these devices may be relatively old, but they are still capable and still transmitting. This means our potential clients may have been vulnerable to information theft for some time. This also means the vulnerability to compromised communications may still be an issueNow, more than ever, information equals money and stealing information is now even easier. It is estimated that over 250,000 bugging devices are sold every year in the UK. There are hundreds of spy shop businesses across the UK, all prospering by selling bugging equipment. This begs the question: where are all these bugs going?Substantial corporate transactions, expansion plans, sensitive appointments and legal mediation regularly take place in hotels, meeting facilities, boardrooms, private homes, vehicles, even yachts and planes.Who are these eaves droppers? The list can include competitors, intrusive agencies, criminals, activists, unscrupulous journalists, opportunists and anyone who has an interest in accessing time or market- sensitive information.However, unauthorised the unauthorised access and compromise of communications has been made easier due to the fast paced advances of electronic eavesdropping devices (or bugs).In these days of globalised business communications, information is the key to success.
 0207 781 9247
0207 781 9247